Microsoft 365, Identity & Device Management
Microsoft 365, Identity & Device Management
Microsoft 365, Identity & Device Management
Microsoft 365, Identity & Device Management
Proactive IT support, monitoring, and management for businesses that want fewer problems, predictable costs, and a partner who takes ownership.
Secure identity, managed devices, and Microsoft 365 configured the right way from day one.
Proactive IT support, monitoring, and management for businesses that want fewer problems, predictable costs, and a partner who takes ownership.
Proactive IT support, monitoring, and management for businesses that want fewer problems, predictable costs, and a partner who takes ownership.
Is This Right for Your Business?
Is This Right for Your Business?
This service is a strong fit if most of the following apply:
Growing teams using Microsoft 365
Growing teams using Microsoft 365
Concerned about account security and identity sprawl
Concerned about account security and identity sprawl
Organizations managing devices & remote users
Organizations managing devices & remote users
Leadership that wants security controls
Leadership that wants security controls
What’s Included with Microsoft 365 & Identity Management
Microsoft 365 Setup & Optimization
Licensing, tenant configuration, email, Teams, and SharePoint done right.
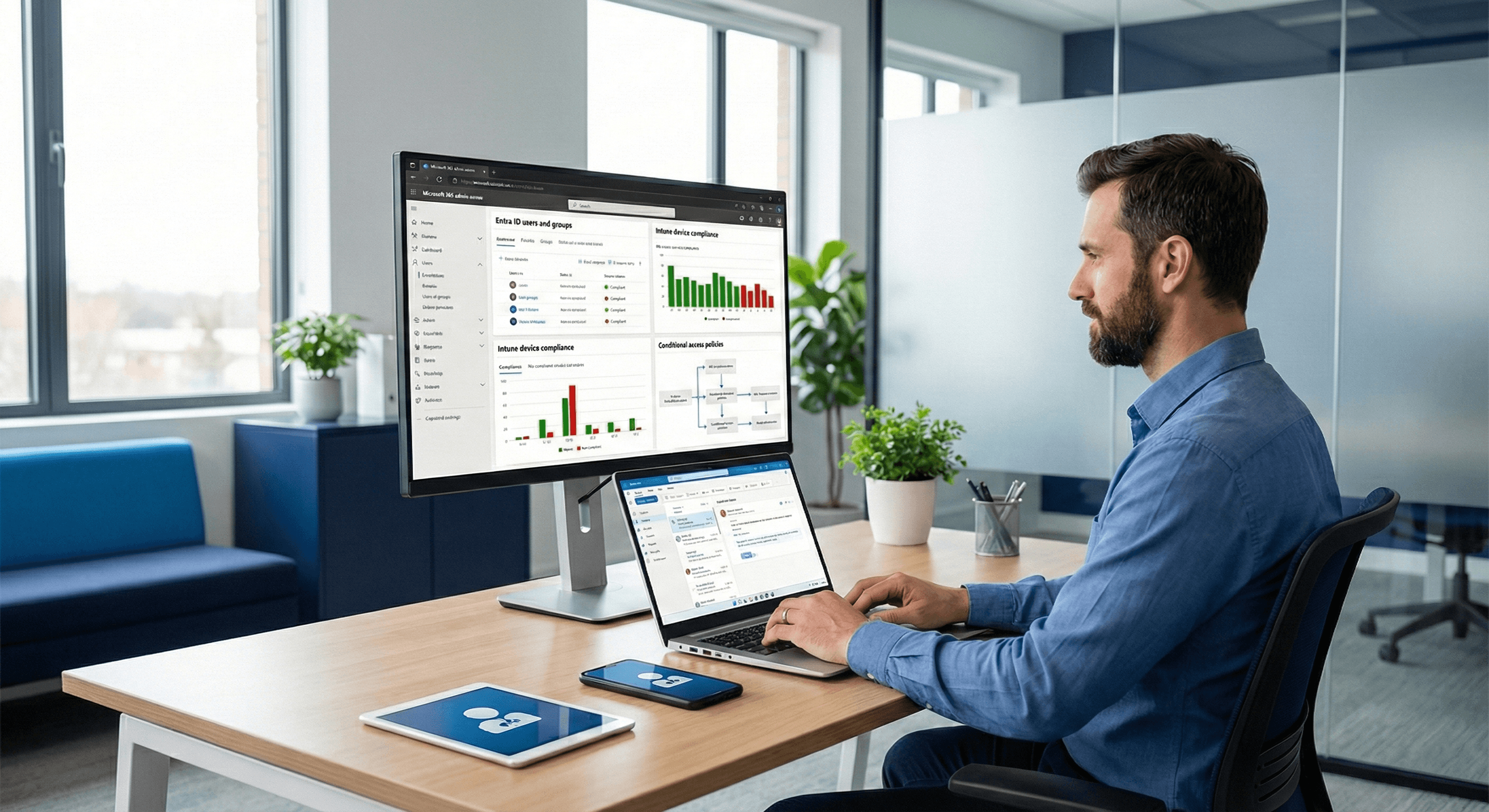
Entra ID (Azure AD) Configuration
Secure identity, role-based access, and conditional access policies.
Multi-Factor Authentication
Strong authentication without frustrating users.
Device Management (Intune)
Laptops and mobile devices secured, compliant, and manageable.
User Provisioning & Offboarding
Consistent onboarding and clean, secure offboarding.
Security Baselines & Policies
Standardized controls that reduce risk across the organization.
Our Approach
Our Approach
A structured, security-first approach to Microsoft environments.
Assess & Standardize
We evaluate your current tenant, devices, and risks.
Secure Identity First
MFA, access controls, and identity hygiene come before anything else.
Deploy & Manage Devices
Devices configured consistently and securely.
Ongoing Oversight
Policies, users, and access continuously reviewed.
Why NextPoint
Direct Access to Expertise
No call centers. Real IT leadership when identity and access matter most.
Clear Accountability
We own security outcomes, not just configurations.
Built for Real Businesses
Practical Microsoft solutions that work in real environments.
Ready to take control of your IT?
Let's simplify your technology and support your business with clarity, reliability, and accountability.
Our Newsletter
Subscribe to our newsletter to get our news delivered to you.
Ready to take control of your IT?
Let's simplify your technology and support your business with clarity, reliability, and accountability.
Our Newsletter
Subscribe to our newsletter to get our news delivered to you.
Ready to take control of your IT?
Let's simplify your technology and support your business with clarity, reliability, and accountability.
Our Newsletter
Subscribe to our newsletter to get our news delivered to you.

